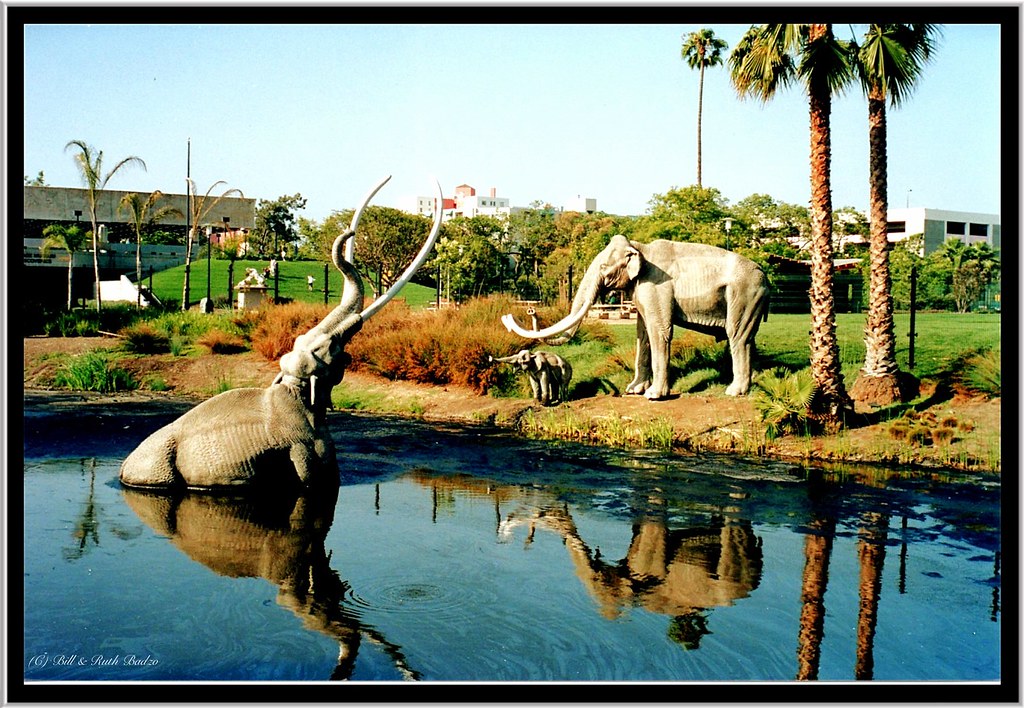
 "Los Angeles CA ~ La Brea Tar Pits" by Onasill ~ Bill Badzo - - 70M Views is licensed under CC BY-NC-ND 2.0
"Los Angeles CA ~ La Brea Tar Pits" by Onasill ~ Bill Badzo - - 70M Views is licensed under CC BY-NC-ND 2.0
I recently completed the SANS SEC503: Network Intrusion Detection course and while there is more than enough information to melt your brain, I picked up a few tricks I'd never seen before. I'd like to share one of the quickest and most practical here.
EndleSSH by Chris Wellens is a tarpit for would be SSH brute force attackers. Clearly in the Active Defense column, EndleSSH works by pretending to be an SSH server, and strings the attempted connections along for near infinite amounts of time.
An automated attack could sit for weeks tied to this connection before realizing something was wrong. Chris has a ton more information on his website above and on his GitHub.
Here's a quick walkthrough:
Configuring EndleSSH on Debian based Droplets
Moving SSH
- To move SSH run the following
sed -i 's/#Port 22/Port $PORTYOUWANT/' /etc/ssh/sshd_config - To restart SSH on the new port
systemctl restart ssh - To verify SSH listening port
netstat -tulpn |grep $PORTYOUWANT
Moving endleSSH
- To disable EndleSSH
systemctl disable endlessh - To allow port of less than 1024.
setcap 'cap_net_bind_service=+ep' /usr/bin/endlessh - To modify config
sed -i 's/#Ambient/Ambient/' /lib/systemd/system/endlessh.service'
sed -i 's/PrivateUsers/#PrivateUsers/ /lib/systemd/system/endlessh.service' - To create new local config
printf "Port 22\nDelay 10000\nMaxLineLength 32\nMaxClients 4096\nLogLevel 0\nBindFamily 0" >> /etc/endlessh/config - Restart EndleSSH
systemctl enable endlessh - Start EndleSSH
systemctl enable endlessh
Modifying FW rules
- List UFW Numbered
ufw status numbered - Delete Old SSH rules
ufw delete $RULENUMBER - Add New SSH rules
ufw allow from $YOURIP to any port $PORTYOUWANT - Add New EndleSSH rules
ufw allow from any to any port 22