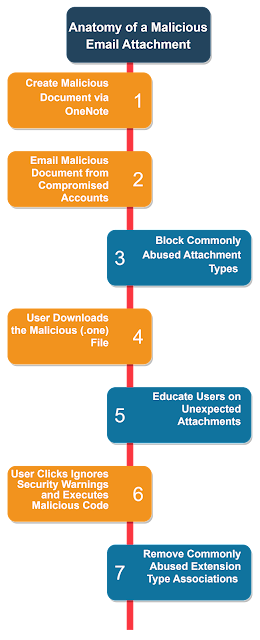
Anatomy of a Malicious Email Attachment
With Microsoft’s recent changes to macros within the Office and M365 suite, Threat Actors have changed their TTPs to utilize the OneNote (.one) file type for Malicious Code Delivery
TL;DR (.one) files are a binary blob capable of embedding any file type. Threat actors are utilizing the prolific nature of OneNote to execute malicious code on endpoints. Block (.one) files from incoming email and dissociate commonly abused file extensions.
The Problem
Microsoft recently modified the way legacy Office applications and M365 applications handle macros within documents. With the restrictions on macros tightening, threat actors have been forced to find new techniques to deliver malicious code to the endpoint.
The Attackers Solution
Microsoft’s OneNote application has two great benefits to an attacker. It’s present anywhere M365 is being used and the application saves files in binary blobs with no limit on file contents.
By targeting the OneNote application, threat actors have identified a prolific and permissive delivery technique.
The Defenders Solution
Microsoft and other email providers offer the opportunity to block incoming file types. Unfortunately, most of these blocks occur based on the named extension of the file, not the file’s header. A secondary control would be to update the Windows extension associations for common file types to an innocuous association. E.g.; .vbs, .bat, .js, .PS1, and others would be associated with notepad.exe. This would prevent execution on-click.
The Anatomy of the Attack
- Attackers create a malicious
.vbsscript* and insert it into a OneNote notebook. They then insert a picture to hide the file, commonly a mock dialogue box reading “Click to allow editing”. Due to OneNotes’ rendering engine, clicking the image will allow the covered malicious file to be activated. - With advancements in commodity phishing kits and the growth of Initial Access Broker markets, emails may come from legitimate trusted contacts who are unaware that their email has been exploited. Additionally, emails from advanced phishing kits may pass DKIM, DMARC, and SPF controls using fully authenticated and secured but misspelled domains. E.g.; Threat actors may send email from bob@p|umbers.com with full SPF/DKIM records though the legitimate domain is plumbers.com
- This is the first opportunity for Defenders to block this attack. Besides ensuring that email is being assessed for SPF/DKIM/DMARC failures, Defenders may choose to block incoming attachment types. Microsoft provides great guidance for completing this within the Exchange Online Protection product. Commonly abused extensions include
.zip,.iso, and.one, as well as common script extensions. - User receives the malicious file and proceeds to download it. Once downloaded, the file will be opened and displayed using OneNote in a manner consistent with the attackers intent; meaning, the malicious script will be hidden behind whichever image the attacker has chosen.
- While an administrative control at best, users should receive continuous training exercises to help educate and practice the skill of identifying malicious attachments.
- OneNote will provide a warning about opening the file. Regardless, users are inundated with these warnings, especially within the M365 suite where Protect View often requires the user to select Enable Editing to interact with a document.
Opening attachments could harm your computer and data.
- To mitigate the execution of the malicious script within a shell commonly abused extension associations may be updated to innocuous applications. E.g.; Associate all common script types with notepad.exe. Home users may protect themselves with via the Windows 10 Settings app while Enterprise users can configure this setting via GPO or MDM, formerly Intune
Advanced Mitigations
User Behavior Analytics
With products that can track the users behavior and assess parent-child app relationships, a model could be generated to prevent the execution of common script types when executed by the OneNote.exe executable.
Hex or Binary Attachment Assessment
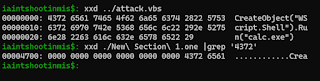
While Windows decides how to treat a file based on the filename extension, some threat actors have been observed instructing victims to rename a file before attempting to execute. This is a common workaround by threat actors and users to circumvent email attachment control. A proper IDS or email filtering application should be able to identify the presence of a (.one) file using the file header e452 5c7b 8cd8 a74d aeb1 5378 d029 96d3.
.one file is a binary blob, the remnants of uncompressed files are accessible as well. In the below screen shot, we can see that 4372 6561 the beginning of CreateObject is available in the .one file at offset 0x4700. A properly defined rule should be able to identify these and other strings within mail attachments.Summary
While threat actors are always seeking out new ways to exploit the user, a simple and straight forward approach to Windows defaults, email attachment protections, and user education can help defeat this attack.